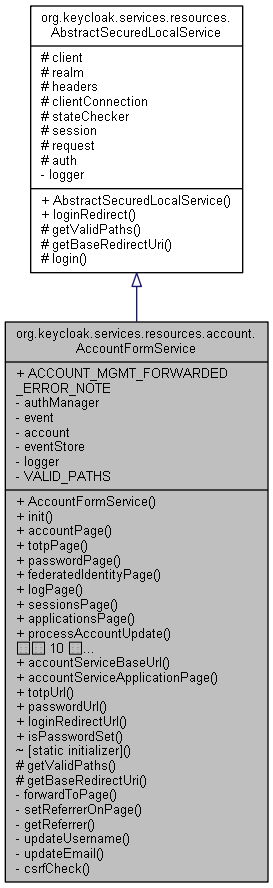
org.keycloak.services.resources.account.AccountFormService の継承関係図
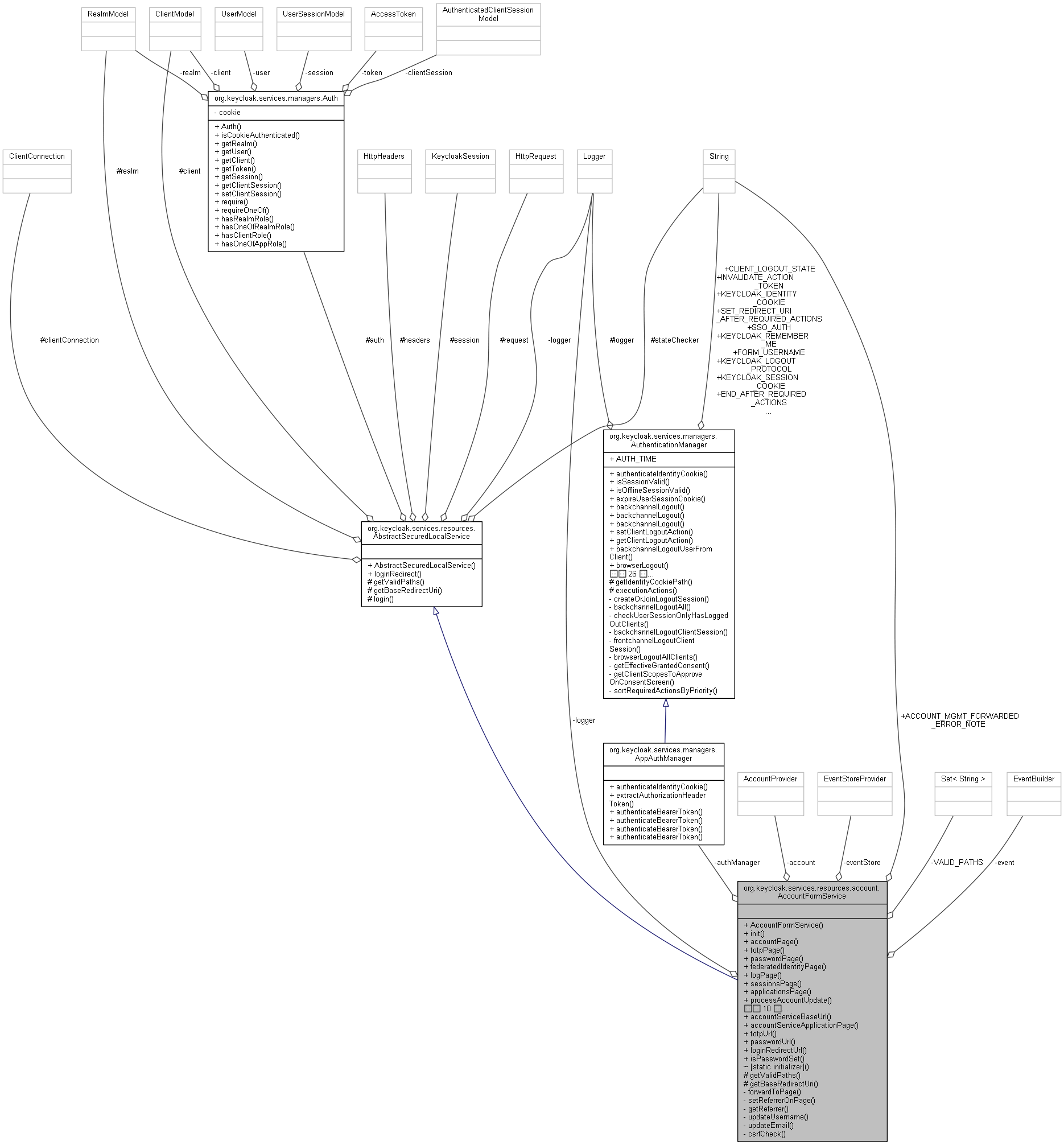
org.keycloak.services.resources.account.AccountFormService 連携図
クラス | |
| enum | AccountSocialAction |
公開メンバ関数 | |
| AccountFormService (RealmModel realm, ClientModel client, EventBuilder event) | |
| void | init () |
| Response | accountPage () |
| Response | totpPage () |
| Response | passwordPage () |
| Response | federatedIdentityPage () |
| Response | logPage () |
| Response | sessionsPage () |
| Response | applicationsPage () |
| Response | processAccountUpdate (final MultivaluedMap< String, String > formData) |
| Response | processSessionsLogout (final MultivaluedMap< String, String > formData) |
| Response | processRevokeGrant (final MultivaluedMap< String, String > formData) |
| Response | processTotpUpdate (final MultivaluedMap< String, String > formData) |
| Response | processPasswordUpdate (final MultivaluedMap< String, String > formData) |
| Response | processFederatedIdentityUpdate (final MultivaluedMap< String, String > formData) |
| Response | resourcesPage (@QueryParam("resource_id") String resourceId) |
| Response | resourceDetailPage (@PathParam("resource_id") String resourceId) |
| Response | grantPermission (@PathParam("resource_id") String resourceId, @FormParam("action") String action, @FormParam("permission_id") String[] permissionId, @FormParam("requester") String requester) |
| Response | shareResource (@PathParam("resource_id") String resourceId, @FormParam("user_id") String[] userIds, @FormParam("scope_id") String[] scopes) |
| Response | processResourceActions (@FormParam("resource_id") String[] resourceIds, @FormParam("action") String action) |
| Response | loginRedirect (@QueryParam("code") String code, @QueryParam("state") String state, @QueryParam("error") String error, @QueryParam("path") String path, @QueryParam("referrer") String referrer, @Context HttpHeaders headers) |
静的公開メンバ関数 | |
| static UriBuilder | accountServiceBaseUrl (UriInfo uriInfo) |
| static UriBuilder | accountServiceApplicationPage (UriInfo uriInfo) |
| static UriBuilder | totpUrl (UriBuilder base) |
| static UriBuilder | passwordUrl (UriBuilder base) |
| static UriBuilder | loginRedirectUrl (UriBuilder base) |
| static boolean | isPasswordSet (KeycloakSession session, RealmModel realm, UserModel user) |
静的公開変数類 | |
| static final String | ACCOUNT_MGMT_FORWARDED_ERROR_NOTE = "ACCOUNT_MGMT_FORWARDED_ERROR" |
限定公開メンバ関数 | |
| Set< String > | getValidPaths () |
| URI | getBaseRedirectUri () |
| Response | login (String path) |
限定公開変数類 | |
| final ClientModel | client |
| RealmModel | realm |
| HttpHeaders | headers |
| ClientConnection | clientConnection |
| String | stateChecker |
| KeycloakSession | session |
| HttpRequest | request |
| Auth | auth |
静的関数 | |
| [static initializer] | |
非公開メンバ関数 | |
| Response | forwardToPage (String path, AccountPages page) |
| void | setReferrerOnPage () |
| String [] | getReferrer () |
| void | updateUsername (String username, UserModel user, KeycloakSession session) |
| void | updateEmail (String email, UserModel user, KeycloakSession session, EventBuilder event) |
| void | csrfCheck (final MultivaluedMap< String, String > formData) |
非公開変数類 | |
| final AppAuthManager | authManager |
| EventBuilder | event |
| AccountProvider | account |
| EventStoreProvider | eventStore |
静的非公開変数類 | |
| static final Logger | logger = Logger.getLogger(AccountFormService.class) |
| static Set< String > | VALID_PATHS = new HashSet<String>() |
詳解
構築子と解体子
◆ AccountFormService()
|
inline |
EventBuilder event
Definition: AccountFormService.java:126
final AppAuthManager authManager
Definition: AccountFormService.java:125
RealmModel realm
Definition: AbstractSecuredLocalService.java:59
final ClientModel client
Definition: AbstractSecuredLocalService.java:58
関数詳解
◆ [static initializer]()
|
inlinestaticpackage |
◆ accountPage()
|
inline |
Get account information.
- 戻り値
Response forwardToPage(String path, AccountPages page)
Definition: AccountFormService.java:191
◆ accountServiceApplicationPage()
|
inlinestatic |
static UriBuilder accountServiceBaseUrl(UriInfo uriInfo)
Definition: AccountFormService.java:178
AccountFormService(RealmModel realm, ClientModel client, EventBuilder event)
Definition: AccountFormService.java:130
◆ accountServiceBaseUrl()
|
inlinestatic |
◆ applicationsPage()
|
inline |
Response forwardToPage(String path, AccountPages page)
Definition: AccountFormService.java:191
◆ csrfCheck()
|
inlineprivate |
◆ federatedIdentityPage()
|
inline |
Response forwardToPage(String path, AccountPages page)
Definition: AccountFormService.java:191
◆ forwardToPage()
|
inlineprivate |
196 return session.getProvider(LoginFormsProvider.class).setError(Messages.NO_ACCESS).createErrorPage(Response.Status.FORBIDDEN);
203 String tabId = request.getUri().getQueryParameters().getFirst(org.keycloak.models.Constants.TAB_ID);
205 AuthenticationSessionModel authSession = new AuthenticationSessionManager(session).getAuthenticationSessionByIdAndClient(realm, userSession.getId(), client, tabId);
211 account.setError(Response.Status.INTERNAL_SERVER_ERROR, errorMessage.getMessage(), errorMessage.getParameters());
Auth auth
Definition: AbstractSecuredLocalService.java:70
Response login(String path)
Definition: AbstractSecuredLocalService.java:132
HttpRequest request
Definition: AbstractSecuredLocalService.java:69
AccountProvider account
Definition: AccountFormService.java:127
static final String ACCOUNT_MGMT_FORWARDED_ERROR_NOTE
Definition: AccountFormService.java:123
KeycloakSession session
Definition: AbstractSecuredLocalService.java:67
RealmModel realm
Definition: AbstractSecuredLocalService.java:59
final ClientModel client
Definition: AbstractSecuredLocalService.java:58
void setReferrerOnPage()
Definition: AccountFormService.java:226
◆ getBaseRedirectUri()
|
inlineprotected |
◆ getReferrer()
|
inlineprivate |
955 String referrerUri = session.getContext().getUri().getQueryParameters().getFirst("referrer_uri");
960 referrerUri = RedirectUtils.verifyRedirectUri(session.getContext().getUri(), referrerUri, realm, referrerClient);
962 referrerUri = ResolveRelative.resolveRelativeUri(session.getContext().getUri().getRequestUri(), client.getRootUrl(), referrerClient.getBaseUrl());
975 referrerUri = RedirectUtils.verifyRedirectUri(session.getContext().getUri(), referrerUri, realm, referrerClient);
KeycloakSession session
Definition: AbstractSecuredLocalService.java:67
RealmModel realm
Definition: AbstractSecuredLocalService.java:59
final ClientModel client
Definition: AbstractSecuredLocalService.java:58
◆ getValidPaths()
|
inlineprotected |
AccountFormService(RealmModel realm, ClientModel client, EventBuilder event)
Definition: AccountFormService.java:130
◆ grantPermission()
|
inline |
721 Resource resource = authorization.getStoreFactory().getResourceStore().findById(resourceId, null);
761 scopesToKeep.add(authorization.getStoreFactory().getScopeStore().findById(id.split(":")[1], client.getId()));
782 filters.put(PermissionTicket.REQUESTER, session.users().getUserByUsername(requester, realm).getId());
790 List<PermissionTicket> tickets = ticketStore.find(filters, resource.getResourceServer().getId(), -1, -1);
797 if (permissionId != null && permissionId.length > 0 && !Arrays.asList(permissionId).contains(ticket.getId())) {
806 if (permissionId != null && permissionId.length > 0 && Arrays.asList(permissionId).contains(ticket.getId())) {
KeycloakSession session
Definition: AbstractSecuredLocalService.java:67
RealmModel realm
Definition: AbstractSecuredLocalService.java:59
final ClientModel client
Definition: AbstractSecuredLocalService.java:58
Response forwardToPage(String path, AccountPages page)
Definition: AccountFormService.java:191
◆ init()
|
inline |
139 account = session.getProvider(AccountProvider.class).setRealm(realm).setUriInfo(session.getContext().getUri()).setHttpHeaders(headers);
141 AuthenticationManager.AuthResult authResult = authManager.authenticateIdentityCookie(session, realm);
144 auth = new Auth(realm, authResult.getToken(), authResult.getUser(), client, authResult.getSession(), true);
165 AuthenticatedClientSessionModel clientSession = userSession.getAuthenticatedClientSessionByClient(client.getId());
167 clientSession = session.sessions().createClientSession(userSession.getRealm(), client, userSession);
175 account.setFeatures(realm.isIdentityFederationEnabled(), eventStore != null && realm.isEventsEnabled(), true, Profile.isFeatureEnabled(Feature.AUTHORIZATION));
EventStoreProvider eventStore
Definition: AccountFormService.java:128
HttpHeaders headers
Definition: AbstractSecuredLocalService.java:62
Auth auth
Definition: AbstractSecuredLocalService.java:70
AuthResult authenticateIdentityCookie(KeycloakSession session, RealmModel realm)
Definition: AppAuthManager.java:35
final AppAuthManager authManager
Definition: AccountFormService.java:125
HttpRequest request
Definition: AbstractSecuredLocalService.java:69
AccountProvider account
Definition: AccountFormService.java:127
KeycloakSession session
Definition: AbstractSecuredLocalService.java:67
RealmModel realm
Definition: AbstractSecuredLocalService.java:59
final ClientModel client
Definition: AbstractSecuredLocalService.java:58
void setClientSession(AuthenticatedClientSessionModel clientSession)
Definition: Auth.java:79
String stateChecker
Definition: AbstractSecuredLocalService.java:65
◆ isPasswordSet()
|
inlinestatic |
KeycloakSession session
Definition: AbstractSecuredLocalService.java:67
RealmModel realm
Definition: AbstractSecuredLocalService.java:59
◆ login()
|
inlineprotectedinherited |
134 String authUrl = OIDCLoginProtocolService.authUrl(session.getContext().getUri()).build(realm.getName()).toString();
152 String referrerUri = session.getContext().getUri().getQueryParameters().getFirst("referrer_uri");
abstract URI getBaseRedirectUri()
ClientConnection clientConnection
Definition: AbstractSecuredLocalService.java:64
KeycloakSession session
Definition: AbstractSecuredLocalService.java:67
RealmModel realm
Definition: AbstractSecuredLocalService.java:59
final ClientModel client
Definition: AbstractSecuredLocalService.java:58
◆ loginRedirect()
|
inlineinherited |
90 return session.getProvider(LoginFormsProvider.class).setError(Messages.NO_ACCESS).createErrorPage(Response.Status.FORBIDDEN);
abstract URI getBaseRedirectUri()
static final Logger logger
Definition: AbstractSecuredLocalService.java:56
KeycloakSession session
Definition: AbstractSecuredLocalService.java:67
RealmModel realm
Definition: AbstractSecuredLocalService.java:59
final ClientModel client
Definition: AbstractSecuredLocalService.java:58
abstract Set< String > getValidPaths()
◆ loginRedirectUrl()
|
inlinestatic |
AccountFormService(RealmModel realm, ClientModel client, EventBuilder event)
Definition: AccountFormService.java:130
◆ logPage()
|
inline |
278 List<Event> events = eventStore.createQuery().type(Constants.EXPOSED_LOG_EVENTS).user(auth.getUser().getId()).maxResults(30).getResultList();
EventStoreProvider eventStore
Definition: AccountFormService.java:128
Auth auth
Definition: AbstractSecuredLocalService.java:70
AccountProvider account
Definition: AccountFormService.java:127
Response forwardToPage(String path, AccountPages page)
Definition: AccountFormService.java:191
◆ passwordPage()
|
inline |
Auth auth
Definition: AbstractSecuredLocalService.java:70
static boolean isPasswordSet(KeycloakSession session, RealmModel realm, UserModel user)
Definition: AccountFormService.java:945
AccountProvider account
Definition: AccountFormService.java:127
KeycloakSession session
Definition: AbstractSecuredLocalService.java:67
RealmModel realm
Definition: AbstractSecuredLocalService.java:59
Response forwardToPage(String path, AccountPages page)
Definition: AccountFormService.java:191
◆ passwordUrl()
|
inlinestatic |
AccountFormService(RealmModel realm, ClientModel client, EventBuilder event)
Definition: AccountFormService.java:130
◆ processAccountUpdate()
|
inline |
Update account information.
Form params:
firstName lastName email
- 引数
-
formData
- 戻り値
346 return account.setErrors(Response.Status.BAD_REQUEST, errors).setProfileFormData(formData).createResponse(AccountPages.ACCOUNT);
364 return account.setError(Response.Status.BAD_REQUEST, Messages.READ_ONLY_USER).setProfileFormData(formData).createResponse(AccountPages.ACCOUNT);
367 return account.setError(Response.Status.CONFLICT, mde.getMessage()).setProfileFormData(formData).createResponse(AccountPages.ACCOUNT);
void csrfCheck(final MultivaluedMap< String, String > formData)
Definition: AccountFormService.java:1048
void updateEmail(String email, UserModel user, KeycloakSession session, EventBuilder event)
Definition: AccountFormService.java:1019
Auth auth
Definition: AbstractSecuredLocalService.java:70
Response login(String path)
Definition: AbstractSecuredLocalService.java:132
EventBuilder event
Definition: AccountFormService.java:126
AccountProvider account
Definition: AccountFormService.java:127
KeycloakSession session
Definition: AbstractSecuredLocalService.java:67
RealmModel realm
Definition: AbstractSecuredLocalService.java:59
void setReferrerOnPage()
Definition: AccountFormService.java:226
void updateUsername(String username, UserModel user, KeycloakSession session)
Definition: AccountFormService.java:1002
◆ processFederatedIdentityUpdate()
|
inline |
624 return account.setError(Response.Status.BAD_REQUEST, Messages.MISSING_IDENTITY_PROVIDER).createResponse(AccountPages.FEDERATED_IDENTITY);
629 return account.setError(Response.Status.BAD_REQUEST, Messages.INVALID_FEDERATED_IDENTITY_ACTION).createResponse(AccountPages.FEDERATED_IDENTITY);
642 return account.setError(Response.Status.BAD_REQUEST, Messages.IDENTITY_PROVIDER_NOT_FOUND).createResponse(AccountPages.FEDERATED_IDENTITY);
647 return account.setError(Response.Status.BAD_REQUEST, Messages.ACCOUNT_DISABLED).createResponse(AccountPages.FEDERATED_IDENTITY);
652 String redirectUri = UriBuilder.fromUri(Urls.accountFederatedIdentityPage(session.getContext().getUri().getBaseUri(), realm.getName())).build().toString();
660 URI linkUrl = Urls.identityProviderLinkRequest(this.session.getContext().getUri().getBaseUri(), providerId, realm.getName());
671 return account.setError(Response.Status.INTERNAL_SERVER_ERROR, Messages.IDENTITY_PROVIDER_REDIRECT_ERROR).createResponse(AccountPages.FEDERATED_IDENTITY);
677 // Removing last social provider is not possible if you don't have other possibility to authenticate
678 if (session.users().getFederatedIdentities(user, realm).size() > 1 || user.getFederationLink() != null || isPasswordSet(session, realm, user)) {
681 logger.debugv("Social provider {0} removed successfully from user {1}", providerId, user.getUsername());
690 return account.setSuccess(Messages.IDENTITY_PROVIDER_REMOVED).createResponse(AccountPages.FEDERATED_IDENTITY);
693 return account.setError(Response.Status.BAD_REQUEST, Messages.FEDERATED_IDENTITY_REMOVING_LAST_PROVIDER).createResponse(AccountPages.FEDERATED_IDENTITY);
697 return account.setError(Response.Status.BAD_REQUEST, Messages.FEDERATED_IDENTITY_NOT_ACTIVE).createResponse(AccountPages.FEDERATED_IDENTITY);
static final Logger logger
Definition: AccountFormService.java:110
void csrfCheck(final MultivaluedMap< String, String > formData)
Definition: AccountFormService.java:1048
Auth auth
Definition: AbstractSecuredLocalService.java:70
Response login(String path)
Definition: AbstractSecuredLocalService.java:132
static boolean isPasswordSet(KeycloakSession session, RealmModel realm, UserModel user)
Definition: AccountFormService.java:945
AccountProvider account
Definition: AccountFormService.java:127
KeycloakSession session
Definition: AbstractSecuredLocalService.java:67
RealmModel realm
Definition: AbstractSecuredLocalService.java:59
final ClientModel client
Definition: AbstractSecuredLocalService.java:58
void setReferrerOnPage()
Definition: AccountFormService.java:226
◆ processPasswordUpdate()
|
inline |
Update account password
Form params:
password - old password password-new pasword-confirm
- 引数
-
formData
- 戻り値
553 return account.setError(Response.Status.BAD_REQUEST, Messages.MISSING_PASSWORD).createResponse(AccountPages.PASSWORD);
560 return account.setError(Response.Status.BAD_REQUEST, Messages.INVALID_PASSWORD_EXISTING).createResponse(AccountPages.PASSWORD);
567 return account.setError(Response.Status.BAD_REQUEST, Messages.MISSING_PASSWORD).createResponse(AccountPages.PASSWORD);
573 return account.setError(Response.Status.BAD_REQUEST, Messages.INVALID_PASSWORD_CONFIRM).createResponse(AccountPages.PASSWORD);
577 session.userCredentialManager().updateCredential(realm, user, UserCredentialModel.password(passwordNew, false));
581 return account.setError(Response.Status.BAD_REQUEST, Messages.READ_ONLY_PASSWORD).createResponse(AccountPages.PASSWORD);
586 return account.setError(Response.Status.INTERNAL_SERVER_ERROR, me.getMessage(), me.getParameters()).createResponse(AccountPages.PASSWORD);
591 return account.setError(Response.Status.INTERNAL_SERVER_ERROR, ape.getMessage()).createResponse(AccountPages.PASSWORD);
597 AuthenticationManager.backchannelLogout(session, realm, s, session.getContext().getUri(), clientConnection, headers, true);
604 return account.setPasswordSet(true).setSuccess(Messages.ACCOUNT_PASSWORD_UPDATED).createResponse(AccountPages.PASSWORD);
void csrfCheck(final MultivaluedMap< String, String > formData)
Definition: AccountFormService.java:1048
HttpHeaders headers
Definition: AbstractSecuredLocalService.java:62
Auth auth
Definition: AbstractSecuredLocalService.java:70
Response login(String path)
Definition: AbstractSecuredLocalService.java:132
static boolean isPasswordSet(KeycloakSession session, RealmModel realm, UserModel user)
Definition: AccountFormService.java:945
ClientConnection clientConnection
Definition: AbstractSecuredLocalService.java:64
AccountProvider account
Definition: AccountFormService.java:127
KeycloakSession session
Definition: AbstractSecuredLocalService.java:67
RealmModel realm
Definition: AbstractSecuredLocalService.java:59
void setReferrerOnPage()
Definition: AccountFormService.java:226
◆ processResourceActions()
|
inline |
911 Resource resource = authorization.getStoreFactory().getResourceStore().findById(resourceId, null);
928 for (PermissionTicket ticket : ticketStore.find(filters, resource.getResourceServer().getId(), -1, -1)) {
Auth auth
Definition: AbstractSecuredLocalService.java:70
KeycloakSession session
Definition: AbstractSecuredLocalService.java:67
Response forwardToPage(String path, AccountPages page)
Definition: AccountFormService.java:191
◆ processRevokeGrant()
|
inline |
415 return account.setError(Response.Status.BAD_REQUEST, Messages.CLIENT_NOT_FOUND).createResponse(AccountPages.APPLICATIONS);
419 return account.setError(Response.Status.BAD_REQUEST, Messages.CLIENT_NOT_FOUND).createResponse(AccountPages.APPLICATIONS);
428 AuthenticationManager.backchannelLogoutUserFromClient(session, realm, user, client, session.getContext().getUri(), headers);
430 event.event(EventType.REVOKE_GRANT).client(auth.getClient()).user(auth.getUser()).detail(Details.REVOKED_CLIENT, client.getClientId()).success();
433 UriBuilder builder = Urls.accountBase(session.getContext().getUri().getBaseUri()).path(AccountFormService.class, "applicationsPage");
void csrfCheck(final MultivaluedMap< String, String > formData)
Definition: AccountFormService.java:1048
HttpHeaders headers
Definition: AbstractSecuredLocalService.java:62
Auth auth
Definition: AbstractSecuredLocalService.java:70
Response login(String path)
Definition: AbstractSecuredLocalService.java:132
AccountProvider account
Definition: AccountFormService.java:127
KeycloakSession session
Definition: AbstractSecuredLocalService.java:67
RealmModel realm
Definition: AbstractSecuredLocalService.java:59
final ClientModel client
Definition: AbstractSecuredLocalService.java:58
void setReferrerOnPage()
Definition: AccountFormService.java:226
AccountFormService(RealmModel realm, ClientModel client, EventBuilder event)
Definition: AccountFormService.java:130
◆ processSessionsLogout()
|
inline |
383 // Rather decrease time a bit. To avoid situation when user is immediatelly redirected to login screen, then automatically authenticated (eg. with Kerberos) and then seeing issues due the stale token
389 AuthenticationManager.backchannelLogout(session, realm, userSession, session.getContext().getUri(), clientConnection, headers, true);
392 UriBuilder builder = Urls.accountBase(session.getContext().getUri().getBaseUri()).path(AccountFormService.class, "sessionsPage");
void csrfCheck(final MultivaluedMap< String, String > formData)
Definition: AccountFormService.java:1048
HttpHeaders headers
Definition: AbstractSecuredLocalService.java:62
Auth auth
Definition: AbstractSecuredLocalService.java:70
Response login(String path)
Definition: AbstractSecuredLocalService.java:132
ClientConnection clientConnection
Definition: AbstractSecuredLocalService.java:64
KeycloakSession session
Definition: AbstractSecuredLocalService.java:67
RealmModel realm
Definition: AbstractSecuredLocalService.java:59
AccountFormService(RealmModel realm, ClientModel client, EventBuilder event)
Definition: AccountFormService.java:130
◆ processTotpUpdate()
|
inline |
Update the TOTP for this account.
form parameters:
totp - otp generated by authenticator totpSecret - totp secret to register
- 引数
-
formData
- 戻り値
464 account.setAttribute("mode", session.getContext().getUri().getQueryParameters().getFirst("mode"));
489 return account.setError(Response.Status.BAD_REQUEST, Messages.MISSING_TOTP).createResponse(AccountPages.TOTP);
492 return account.setError(Response.Status.BAD_REQUEST, Messages.INVALID_TOTP).createResponse(AccountPages.TOTP);
void csrfCheck(final MultivaluedMap< String, String > formData)
Definition: AccountFormService.java:1048
Auth auth
Definition: AbstractSecuredLocalService.java:70
Response login(String path)
Definition: AbstractSecuredLocalService.java:132
AccountProvider account
Definition: AccountFormService.java:127
KeycloakSession session
Definition: AbstractSecuredLocalService.java:67
RealmModel realm
Definition: AbstractSecuredLocalService.java:59
void setReferrerOnPage()
Definition: AccountFormService.java:226
◆ resourceDetailPage()
|
inline |
Response forwardToPage(String path, AccountPages page)
Definition: AccountFormService.java:191
◆ resourcesPage()
|
inline |
Response forwardToPage(String path, AccountPages page)
Definition: AccountFormService.java:191
◆ sessionsPage()
|
inline |
Auth auth
Definition: AbstractSecuredLocalService.java:70
AccountProvider account
Definition: AccountFormService.java:127
KeycloakSession session
Definition: AbstractSecuredLocalService.java:67
RealmModel realm
Definition: AbstractSecuredLocalService.java:59
Response forwardToPage(String path, AccountPages page)
Definition: AccountFormService.java:191
◆ setReferrerOnPage()
|
inlineprivate |
String [] getReferrer()
Definition: AccountFormService.java:949
AccountProvider account
Definition: AccountFormService.java:127
◆ shareResource()
|
inline |
829 Resource resource = authorization.getStoreFactory().getResourceStore().findById(resourceId, null);
836 return account.setError(Status.BAD_REQUEST, Messages.MISSING_PASSWORD).createResponse(AccountPages.PASSWORD);
851 return account.setError(Status.BAD_REQUEST, Messages.INVALID_USER).createResponse(AccountPages.RESOURCE_DETAIL);
860 List<PermissionTicket> tickets = ticketStore.find(filters, resource.getResourceServer().getId(), -1, -1);
865 PermissionTicket ticket = ticketStore.create(resourceId, scope, user.getId(), resource.getResourceServer());
870 PermissionTicket ticket = ticketStore.create(resourceId, null, user.getId(), resource.getResourceServer());
874 PermissionTicket ticket = ticketStore.create(resourceId, scope.getId(), user.getId(), resource.getResourceServer());
891 PermissionTicket ticket = ticketStore.create(resourceId, grantScope, user.getId(), resource.getResourceServer());
Auth auth
Definition: AbstractSecuredLocalService.java:70
AccountProvider account
Definition: AccountFormService.java:127
KeycloakSession session
Definition: AbstractSecuredLocalService.java:67
RealmModel realm
Definition: AbstractSecuredLocalService.java:59
Response forwardToPage(String path, AccountPages page)
Definition: AccountFormService.java:191
◆ totpPage()
|
inline |
251 account.setAttribute("mode", session.getContext().getUri().getQueryParameters().getFirst("mode"));
AccountProvider account
Definition: AccountFormService.java:127
KeycloakSession session
Definition: AbstractSecuredLocalService.java:67
Response forwardToPage(String path, AccountPages page)
Definition: AccountFormService.java:191
◆ totpUrl()
|
inlinestatic |
AccountFormService(RealmModel realm, ClientModel client, EventBuilder event)
Definition: AccountFormService.java:130
◆ updateEmail()
|
inlineprivate |
◆ updateUsername()
|
inlineprivate |
KeycloakSession session
Definition: AbstractSecuredLocalService.java:67
RealmModel realm
Definition: AbstractSecuredLocalService.java:59
メンバ詳解
◆ account
|
private |
◆ ACCOUNT_MGMT_FORWARDED_ERROR_NOTE
|
static |
◆ auth
|
protectedinherited |
◆ authManager
|
private |
◆ client
|
protectedinherited |
◆ clientConnection
|
protectedinherited |
◆ event
|
private |
◆ eventStore
|
private |
◆ headers
|
protectedinherited |
◆ logger
|
staticprivate |
◆ realm
|
protectedinherited |
◆ request
|
protectedinherited |
◆ session
|
protectedinherited |
◆ stateChecker
|
protectedinherited |
◆ VALID_PATHS
|
staticprivate |
このクラス詳解は次のファイルから抽出されました:
- D:/AppData/doxygen/keycloak/rest-service/src/services/src/main/java/org/keycloak/services/resources/account/AccountFormService.java
 1.8.13
1.8.13