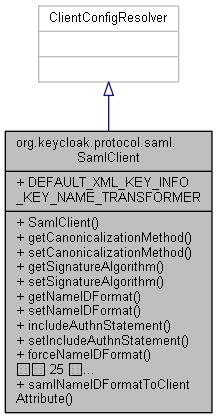
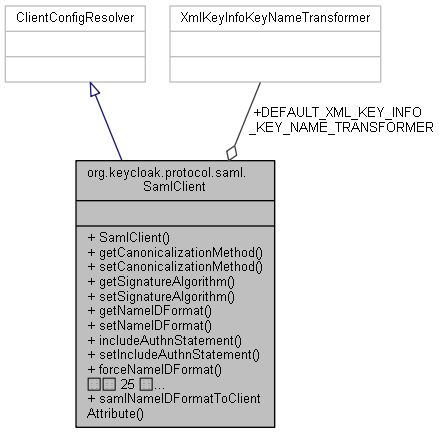
Configuration of a SAML-enabled client.
- 著者
- Bill Burke
- バージョン
- Revision
- 1
◆ SamlClient()
| org.keycloak.protocol.saml.SamlClient.SamlClient |
( |
ClientModel |
client | ) |
|
|
inline |
◆ addExtensionsElementWithKeyInfo()
| boolean org.keycloak.protocol.saml.SamlClient.addExtensionsElementWithKeyInfo |
( |
| ) |
|
|
inline |
128 return "true".equals(resolveAttribute(SamlConfigAttributes.SAML_SERVER_SIGNATURE_KEYINFO_EXT));
◆ forceNameIDFormat()
| boolean org.keycloak.protocol.saml.SamlClient.forceNameIDFormat |
( |
| ) |
|
|
inline |
111 return "true".equals(resolveAttribute(SamlConfigAttributes.SAML_FORCE_NAME_ID_FORMAT_ATTRIBUTE));
◆ forcePostBinding()
| boolean org.keycloak.protocol.saml.SamlClient.forcePostBinding |
( |
| ) |
|
|
inline |
136 return "true".equals(resolveAttribute(SamlConfigAttributes.SAML_FORCE_POST_BINDING));
◆ getCanonicalizationMethod()
| String org.keycloak.protocol.saml.SamlClient.getCanonicalizationMethod |
( |
| ) |
|
|
inline |
41 return resolveAttribute(SamlConfigAttributes.SAML_CANONICALIZATION_METHOD_ATTRIBUTE);
◆ getClientEncryptingCertificate()
| String org.keycloak.protocol.saml.SamlClient.getClientEncryptingCertificate |
( |
| ) |
|
|
inline |
191 return client.getAttribute(SamlConfigAttributes.SAML_ENCRYPTION_CERTIFICATE_ATTRIBUTE);
◆ getClientEncryptingPrivateKey()
| String org.keycloak.protocol.saml.SamlClient.getClientEncryptingPrivateKey |
( |
| ) |
|
|
inline |
200 return client.getAttribute(SamlConfigAttributes.SAML_ENCRYPTION_PRIVATE_KEY_ATTRIBUTE);
◆ getClientSigningCertificate()
| String org.keycloak.protocol.saml.SamlClient.getClientSigningCertificate |
( |
| ) |
|
|
inline |
173 return client.getAttribute(SamlConfigAttributes.SAML_SIGNING_CERTIFICATE_ATTRIBUTE);
◆ getClientSigningPrivateKey()
| String org.keycloak.protocol.saml.SamlClient.getClientSigningPrivateKey |
( |
| ) |
|
|
inline |
182 return client.getAttribute(SamlConfigAttributes.SAML_SIGNING_PRIVATE_KEY);
◆ getNameIDFormat()
| String org.keycloak.protocol.saml.SamlClient.getNameIDFormat |
( |
| ) |
|
|
inline |
63 String nameIdFormat = null;
65 String configuredNameIdFormat = resolveAttribute(SamlConfigAttributes.SAML_NAME_ID_FORMAT_ATTRIBUTE);
66 if (configuredNameIdFormat != null) {
67 if (configuredNameIdFormat.equals(
"email")) {
68 nameIdFormat = JBossSAMLURIConstants.NAMEID_FORMAT_EMAIL.get();
69 }
else if (configuredNameIdFormat.equals(
"persistent")) {
70 nameIdFormat = JBossSAMLURIConstants.NAMEID_FORMAT_PERSISTENT.get();
71 }
else if (configuredNameIdFormat.equals(
"transient")) {
72 nameIdFormat = JBossSAMLURIConstants.NAMEID_FORMAT_TRANSIENT.get();
73 }
else if (configuredNameIdFormat.equals(
"username")) {
74 nameIdFormat = JBossSAMLURIConstants.NAMEID_FORMAT_UNSPECIFIED.get();
76 nameIdFormat = JBossSAMLURIConstants.NAMEID_FORMAT_UNSPECIFIED.get();
◆ getSignatureAlgorithm()
| SignatureAlgorithm org.keycloak.protocol.saml.SamlClient.getSignatureAlgorithm |
( |
| ) |
|
|
inline |
49 String alg = resolveAttribute(SamlConfigAttributes.SAML_SIGNATURE_ALGORITHM);
51 SignatureAlgorithm algorithm = SignatureAlgorithm.valueOf(alg);
52 if (algorithm != null)
55 return SignatureAlgorithm.RSA_SHA256;
◆ getXmlSigKeyInfoKeyNameTransformer()
| XmlKeyInfoKeyNameTransformer org.keycloak.protocol.saml.SamlClient.getXmlSigKeyInfoKeyNameTransformer |
( |
| ) |
|
|
inline |
Always returns non-
result.
- 戻り値
- Configured ransformer of DEFAULT_XML_KEY_INFO_KEY_NAME_TRANSFORMER if not set.
214 return XmlKeyInfoKeyNameTransformer.from(
215 client.getAttribute(SamlConfigAttributes.SAML_SERVER_SIGNATURE_KEYINFO_KEY_NAME_TRANSFORMER),
static final XmlKeyInfoKeyNameTransformer DEFAULT_XML_KEY_INFO_KEY_NAME_TRANSFORMER
Definition: SamlClient.java:34
◆ includeAuthnStatement()
| boolean org.keycloak.protocol.saml.SamlClient.includeAuthnStatement |
( |
| ) |
|
|
inline |
103 return "true".equals(resolveAttribute(SamlConfigAttributes.SAML_AUTHNSTATEMENT));
◆ includeOneTimeUseCondition()
| boolean org.keycloak.protocol.saml.SamlClient.includeOneTimeUseCondition |
( |
| ) |
|
|
inline |
227 return "true".equals(resolveAttribute(SamlConfigAttributes.SAML_ONETIMEUSE_CONDITION));
◆ requiresAssertionSignature()
| boolean org.keycloak.protocol.saml.SamlClient.requiresAssertionSignature |
( |
| ) |
|
|
inline |
145 return "true".equals(resolveAttribute(SamlConfigAttributes.SAML_ASSERTION_SIGNATURE));
◆ requiresClientSignature()
| boolean org.keycloak.protocol.saml.SamlClient.requiresClientSignature |
( |
| ) |
|
|
inline |
164 return "true".equals(resolveAttribute(SamlConfigAttributes.SAML_CLIENT_SIGNATURE_ATTRIBUTE));
◆ requiresEncryption()
| boolean org.keycloak.protocol.saml.SamlClient.requiresEncryption |
( |
| ) |
|
|
inline |
154 return "true".equals(resolveAttribute(SamlConfigAttributes.SAML_ENCRYPT));
◆ requiresRealmSignature()
| boolean org.keycloak.protocol.saml.SamlClient.requiresRealmSignature |
( |
| ) |
|
|
inline |
120 return "true".equals(resolveAttribute(SamlConfigAttributes.SAML_SERVER_SIGNATURE));
◆ samlNameIDFormatToClientAttribute()
| static String org.keycloak.protocol.saml.SamlClient.samlNameIDFormatToClientAttribute |
( |
String |
nameIdFormat | ) |
|
|
inlinestatic |
84 if (nameIdFormat.equals(JBossSAMLURIConstants.NAMEID_FORMAT_EMAIL.get())) {
86 }
else if (nameIdFormat.equals(JBossSAMLURIConstants.NAMEID_FORMAT_PERSISTENT.get())) {
88 }
else if (nameIdFormat.equals(JBossSAMLURIConstants.NAMEID_FORMAT_TRANSIENT.get())) {
90 }
else if (nameIdFormat.equals(JBossSAMLURIConstants.NAMEID_FORMAT_UNSPECIFIED.get())) {
◆ setAddExtensionsElementWithKeyInfo()
| void org.keycloak.protocol.saml.SamlClient.setAddExtensionsElementWithKeyInfo |
( |
boolean |
val | ) |
|
|
inline |
132 client.setAttribute(SamlConfigAttributes.SAML_SERVER_SIGNATURE_KEYINFO_EXT, Boolean.toString(val));
◆ setCanonicalizationMethod()
| void org.keycloak.protocol.saml.SamlClient.setCanonicalizationMethod |
( |
String |
value | ) |
|
|
inline |
45 client.setAttribute(SamlConfigAttributes.SAML_CANONICALIZATION_METHOD_ATTRIBUTE, value);
◆ setClientEncryptingCertificate()
| void org.keycloak.protocol.saml.SamlClient.setClientEncryptingCertificate |
( |
String |
val | ) |
|
|
inline |
195 client.setAttribute(SamlConfigAttributes.SAML_ENCRYPTION_CERTIFICATE_ATTRIBUTE, val);
◆ setClientEncryptingPrivateKey()
| void org.keycloak.protocol.saml.SamlClient.setClientEncryptingPrivateKey |
( |
String |
val | ) |
|
|
inline |
204 client.setAttribute(SamlConfigAttributes.SAML_ENCRYPTION_PRIVATE_KEY_ATTRIBUTE, val);
◆ setClientSigningCertificate()
| void org.keycloak.protocol.saml.SamlClient.setClientSigningCertificate |
( |
String |
val | ) |
|
|
inline |
177 client.setAttribute(SamlConfigAttributes.SAML_SIGNING_CERTIFICATE_ATTRIBUTE, val);
◆ setClientSigningPrivateKey()
| void org.keycloak.protocol.saml.SamlClient.setClientSigningPrivateKey |
( |
String |
val | ) |
|
|
inline |
186 client.setAttribute(SamlConfigAttributes.SAML_SIGNING_PRIVATE_KEY, val);
◆ setForceNameIDFormat()
| void org.keycloak.protocol.saml.SamlClient.setForceNameIDFormat |
( |
boolean |
val | ) |
|
|
inline |
116 client.setAttribute(SamlConfigAttributes.SAML_FORCE_NAME_ID_FORMAT_ATTRIBUTE, Boolean.toString(val));
◆ setForcePostBinding()
| void org.keycloak.protocol.saml.SamlClient.setForcePostBinding |
( |
boolean |
val | ) |
|
|
inline |
140 client.setAttribute(SamlConfigAttributes.SAML_FORCE_POST_BINDING, Boolean.toString(val));
◆ setIncludeAuthnStatement()
| void org.keycloak.protocol.saml.SamlClient.setIncludeAuthnStatement |
( |
boolean |
val | ) |
|
|
inline |
107 client.setAttribute(SamlConfigAttributes.SAML_AUTHNSTATEMENT, Boolean.toString(val));
◆ setIncludeOneTimeUseCondition()
| void org.keycloak.protocol.saml.SamlClient.setIncludeOneTimeUseCondition |
( |
boolean |
val | ) |
|
|
inline |
231 client.setAttribute(SamlConfigAttributes.SAML_ONETIMEUSE_CONDITION, Boolean.toString(val));
◆ setNameIDFormat()
| void org.keycloak.protocol.saml.SamlClient.setNameIDFormat |
( |
String |
format | ) |
|
|
inline |
99 client.setAttribute(SamlConfigAttributes.SAML_NAME_ID_FORMAT_ATTRIBUTE, format);
◆ setRequiresAssertionSignature()
| void org.keycloak.protocol.saml.SamlClient.setRequiresAssertionSignature |
( |
boolean |
val | ) |
|
|
inline |
149 client.setAttribute(SamlConfigAttributes.SAML_ASSERTION_SIGNATURE, Boolean.toString(val));
◆ setRequiresClientSignature()
| void org.keycloak.protocol.saml.SamlClient.setRequiresClientSignature |
( |
boolean |
val | ) |
|
|
inline |
168 client.setAttribute(SamlConfigAttributes.SAML_CLIENT_SIGNATURE_ATTRIBUTE, Boolean.toString(val));
◆ setRequiresEncryption()
| void org.keycloak.protocol.saml.SamlClient.setRequiresEncryption |
( |
boolean |
val | ) |
|
|
inline |
159 client.setAttribute(SamlConfigAttributes.SAML_ENCRYPT, Boolean.toString(val));
◆ setRequiresRealmSignature()
| void org.keycloak.protocol.saml.SamlClient.setRequiresRealmSignature |
( |
boolean |
val | ) |
|
|
inline |
124 client.setAttribute(SamlConfigAttributes.SAML_SERVER_SIGNATURE, Boolean.toString(val));
◆ setSignatureAlgorithm()
| void org.keycloak.protocol.saml.SamlClient.setSignatureAlgorithm |
( |
SignatureAlgorithm |
algorithm | ) |
|
|
inline |
59 client.setAttribute(SamlConfigAttributes.SAML_SIGNATURE_ALGORITHM, algorithm.name());
◆ setXmlSigKeyInfoKeyNameTransformer()
| void org.keycloak.protocol.saml.SamlClient.setXmlSigKeyInfoKeyNameTransformer |
( |
XmlKeyInfoKeyNameTransformer |
xmlSigKeyInfoKeyNameTransformer | ) |
|
|
inline |
220 client.setAttribute(SamlConfigAttributes.SAML_SERVER_SIGNATURE_KEYINFO_KEY_NAME_TRANSFORMER,
221 xmlSigKeyInfoKeyNameTransformer == null
223 : xmlSigKeyInfoKeyNameTransformer.name());
◆ DEFAULT_XML_KEY_INFO_KEY_NAME_TRANSFORMER
| final XmlKeyInfoKeyNameTransformer org.keycloak.protocol.saml.SamlClient.DEFAULT_XML_KEY_INFO_KEY_NAME_TRANSFORMER = XmlKeyInfoKeyNameTransformer.KEY_ID |
|
static |
このクラス詳解は次のファイルから抽出されました:
- D:/AppData/doxygen/keycloak/rest-service/src/services/src/main/java/org/keycloak/protocol/saml/SamlClient.java
 1.8.13
1.8.13