org.keycloak.services.resources.LoginActionsService 連携図
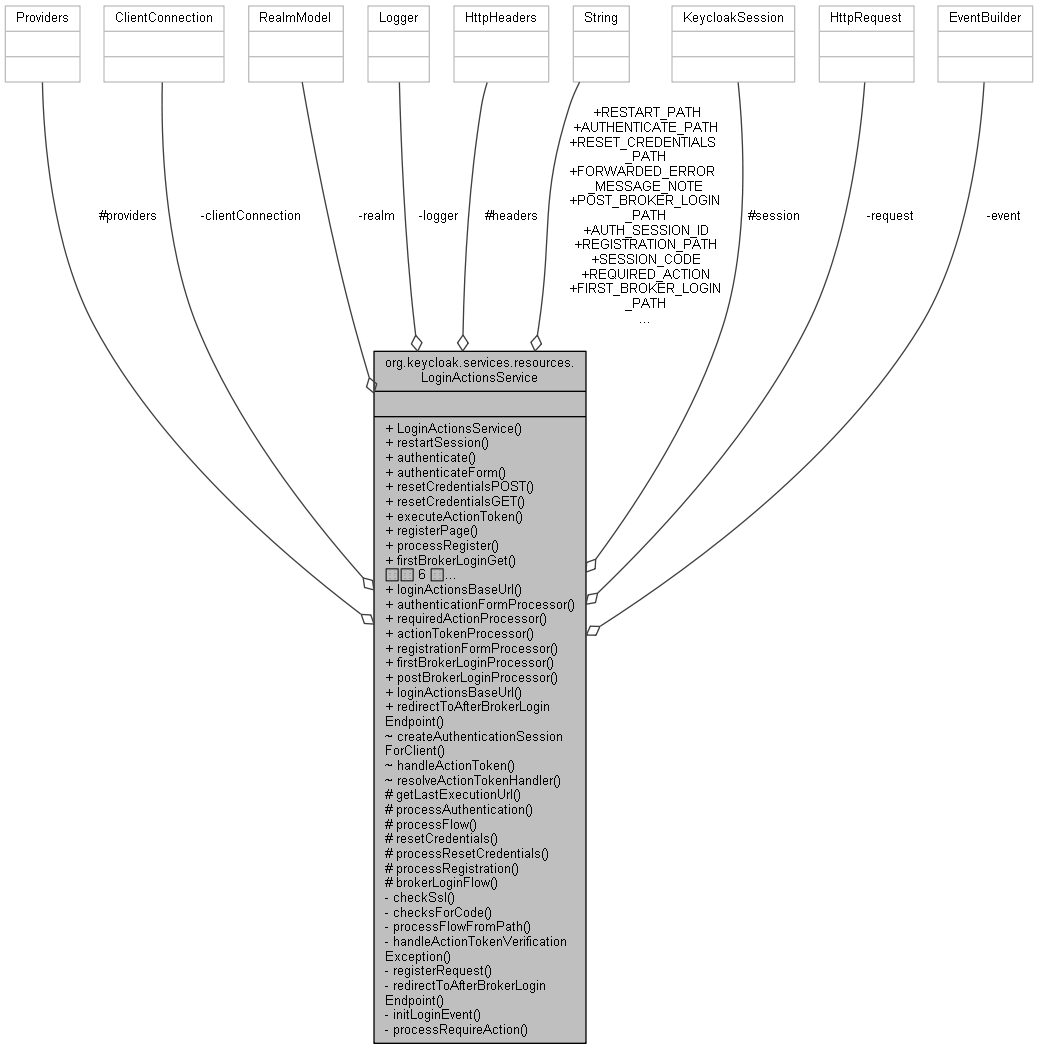
公開メンバ関数 | |
| LoginActionsService (RealmModel realm, EventBuilder event) | |
| Response | restartSession (@QueryParam(AUTH_SESSION_ID) String authSessionId, @QueryParam(Constants.CLIENT_ID) String clientId, @QueryParam(Constants.TAB_ID) String tabId) |
| Response | authenticate (@QueryParam(AUTH_SESSION_ID) String authSessionId, @QueryParam(SESSION_CODE) String code, @QueryParam(Constants.EXECUTION) String execution, @QueryParam(Constants.CLIENT_ID) String clientId, @QueryParam(Constants.TAB_ID) String tabId) |
| Response | authenticateForm (@QueryParam(AUTH_SESSION_ID) String authSessionId, @QueryParam(SESSION_CODE) String code, @QueryParam(Constants.EXECUTION) String execution, @QueryParam(Constants.CLIENT_ID) String clientId, @QueryParam(Constants.TAB_ID) String tabId) |
| Response | resetCredentialsPOST (@QueryParam(AUTH_SESSION_ID) String authSessionId, @QueryParam(SESSION_CODE) String code, @QueryParam(Constants.EXECUTION) String execution, @QueryParam(Constants.CLIENT_ID) String clientId, @QueryParam(Constants.TAB_ID) String tabId, @QueryParam(Constants.KEY) String key) |
| Response | resetCredentialsGET (@QueryParam(AUTH_SESSION_ID) String authSessionId, @QueryParam(SESSION_CODE) String code, @QueryParam(Constants.EXECUTION) String execution, @QueryParam(Constants.CLIENT_ID) String clientId, @QueryParam(Constants.TAB_ID) String tabId) |
| Response | executeActionToken (@QueryParam(AUTH_SESSION_ID) String authSessionId, @QueryParam(Constants.KEY) String key, @QueryParam(Constants.EXECUTION) String execution, @QueryParam(Constants.CLIENT_ID) String clientId, @QueryParam(Constants.TAB_ID) String tabId) |
| Response | registerPage (@QueryParam(AUTH_SESSION_ID) String authSessionId, @QueryParam(SESSION_CODE) String code, @QueryParam(Constants.EXECUTION) String execution, @QueryParam(Constants.CLIENT_ID) String clientId, @QueryParam(Constants.TAB_ID) String tabId) |
| Response | processRegister (@QueryParam(AUTH_SESSION_ID) String authSessionId, @QueryParam(SESSION_CODE) String code, @QueryParam(Constants.EXECUTION) String execution, @QueryParam(Constants.CLIENT_ID) String clientId, @QueryParam(Constants.TAB_ID) String tabId) |
| Response | firstBrokerLoginGet (@QueryParam(AUTH_SESSION_ID) String authSessionId, @QueryParam(SESSION_CODE) String code, @QueryParam(Constants.EXECUTION) String execution, @QueryParam(Constants.CLIENT_ID) String clientId, @QueryParam(Constants.TAB_ID) String tabId) |
| Response | firstBrokerLoginPost (@QueryParam(AUTH_SESSION_ID) String authSessionId, @QueryParam(SESSION_CODE) String code, @QueryParam(Constants.EXECUTION) String execution, @QueryParam(Constants.CLIENT_ID) String clientId, @QueryParam(Constants.TAB_ID) String tabId) |
| Response | postBrokerLoginGet (@QueryParam(AUTH_SESSION_ID) String authSessionId, @QueryParam(SESSION_CODE) String code, @QueryParam(Constants.EXECUTION) String execution, @QueryParam(Constants.CLIENT_ID) String clientId, @QueryParam(Constants.TAB_ID) String tabId) |
| Response | postBrokerLoginPost (@QueryParam(AUTH_SESSION_ID) String authSessionId, @QueryParam(SESSION_CODE) String code, @QueryParam(Constants.EXECUTION) String execution, @QueryParam(Constants.CLIENT_ID) String clientId, @QueryParam(Constants.TAB_ID) String tabId) |
| Response | processConsent (final MultivaluedMap< String, String > formData) |
| Response | requiredActionPOST (@QueryParam(AUTH_SESSION_ID) String authSessionId, @QueryParam(SESSION_CODE) final String code, @QueryParam(Constants.EXECUTION) String action, @QueryParam(Constants.CLIENT_ID) String clientId, @QueryParam(Constants.TAB_ID) String tabId) |
| Response | requiredActionGET (@QueryParam(AUTH_SESSION_ID) String authSessionId, @QueryParam(SESSION_CODE) final String code, @QueryParam(Constants.EXECUTION) String action, @QueryParam(Constants.CLIENT_ID) String clientId, @QueryParam(Constants.TAB_ID) String tabId) |
静的公開メンバ関数 | |
| static UriBuilder | loginActionsBaseUrl (UriInfo uriInfo) |
| static UriBuilder | authenticationFormProcessor (UriInfo uriInfo) |
| static UriBuilder | requiredActionProcessor (UriInfo uriInfo) |
| static UriBuilder | actionTokenProcessor (UriInfo uriInfo) |
| static UriBuilder | registrationFormProcessor (UriInfo uriInfo) |
| static UriBuilder | firstBrokerLoginProcessor (UriInfo uriInfo) |
| static UriBuilder | postBrokerLoginProcessor (UriInfo uriInfo) |
| static UriBuilder | loginActionsBaseUrl (UriBuilder baseUriBuilder) |
| static Response | redirectToAfterBrokerLoginEndpoint (KeycloakSession session, RealmModel realm, UriInfo uriInfo, AuthenticationSessionModel authSession, boolean firstBrokerLogin) |
静的公開変数類 | |
| static final String | AUTHENTICATE_PATH = "authenticate" |
| static final String | REGISTRATION_PATH = "registration" |
| static final String | RESET_CREDENTIALS_PATH = "reset-credentials" |
| static final String | REQUIRED_ACTION = "required-action" |
| static final String | FIRST_BROKER_LOGIN_PATH = "first-broker-login" |
| static final String | POST_BROKER_LOGIN_PATH = "post-broker-login" |
| static final String | RESTART_PATH = "restart" |
| static final String | FORWARDED_ERROR_MESSAGE_NOTE = "forwardedErrorMessage" |
| static final String | SESSION_CODE = "session_code" |
| static final String | AUTH_SESSION_ID = "auth_session_id" |
限定公開メンバ関数 | |
| URI | getLastExecutionUrl (String flowPath, String executionId, String clientId, String tabId) |
| Response | processAuthentication (boolean action, String execution, AuthenticationSessionModel authSession, String errorMessage) |
| Response | processFlow (boolean action, String execution, AuthenticationSessionModel authSession, String flowPath, AuthenticationFlowModel flow, String errorMessage, AuthenticationProcessor processor) |
| Response | resetCredentials (String authSessionId, String code, String execution, String clientId, String tabId) |
| Response | processResetCredentials (boolean actionRequest, String execution, AuthenticationSessionModel authSession, String errorMessage) |
| Response | processRegistration (boolean action, String execution, AuthenticationSessionModel authSession, String errorMessage) |
| Response | brokerLoginFlow (String authSessionId, String code, String execution, String clientId, String tabId, String flowPath) |
限定公開変数類 | |
| HttpHeaders | headers |
| Providers | providers |
| KeycloakSession | session |
関数 | |
| AuthenticationSessionModel | createAuthenticationSessionForClient () throws UriBuilderException, IllegalArgumentException |
| protected< T extends JsonWebToken &ActionTokenKeyModel > Response | handleActionToken (String tokenString, String execution, String clientId, String tabId) |
| private< T extends JsonWebToken > ActionTokenHandler< T > | resolveActionTokenHandler (String actionId) throws VerificationException |
非公開メンバ関数 | |
| boolean | checkSsl () |
| SessionCodeChecks | checksForCode (String authSessionId, String code, String execution, String clientId, String tabId, String flowPath) |
| Response | processFlowFromPath (String flowPath, AuthenticationSessionModel authSession, String errorMessage) |
| Response | handleActionTokenVerificationException (ActionTokenContext<?> tokenContext, VerificationException ex, String eventError, String errorMessage) |
| Response | registerRequest (String authSessionId, String code, String execution, String clientId, String tabId, boolean isPostRequest) |
| Response | redirectToAfterBrokerLoginEndpoint (AuthenticationSessionModel authSession, boolean firstBrokerLogin) |
| void | initLoginEvent (AuthenticationSessionModel authSession) |
| Response | processRequireAction (final String authSessionId, final String code, String action, String clientId, String tabId) |
非公開変数類 | |
| RealmModel | realm |
| HttpRequest | request |
| ClientConnection | clientConnection |
| EventBuilder | event |
静的非公開変数類 | |
| static final Logger | logger = Logger.getLogger(LoginActionsService.class) |
詳解
構築子と解体子
◆ LoginActionsService()
|
inline |
EventBuilder event
Definition: LoginActionsService.java:143
RealmModel realm
Definition: LoginActionsService.java:126
関数詳解
◆ actionTokenProcessor()
|
inlinestatic |
LoginActionsService(RealmModel realm, EventBuilder event)
Definition: LoginActionsService.java:178
static UriBuilder loginActionsBaseUrl(UriInfo uriInfo)
Definition: LoginActionsService.java:145
◆ authenticate()
|
inline |
protocol independent login page entry point
- 引数
-
code
- 戻り値
251 SessionCodeChecks checks = checksForCode(authSessionId, code, execution, clientId, tabId, AUTHENTICATE_PATH);
252 if (!checks.verifyActiveAndValidAction(AuthenticationSessionModel.Action.AUTHENTICATE.name(), ClientSessionCode.ActionType.LOGIN)) {
SessionCodeChecks checksForCode(String authSessionId, String code, String execution, String clientId, String tabId, String flowPath)
Definition: LoginActionsService.java:192
Response processAuthentication(boolean action, String execution, AuthenticationSessionModel authSession, String errorMessage)
Definition: LoginActionsService.java:262
static final String AUTHENTICATE_PATH
Definition: LoginActionsService.java:112
◆ authenticateForm()
|
inline |
URL called after login page. YOU SHOULD NEVER INVOKE THIS DIRECTLY!
- 引数
-
code
- 戻り値
Response authenticate(@QueryParam(AUTH_SESSION_ID) String authSessionId, @QueryParam(SESSION_CODE) String code, @QueryParam(Constants.EXECUTION) String execution, @QueryParam(Constants.CLIENT_ID) String clientId, @QueryParam(Constants.TAB_ID) String tabId)
Definition: LoginActionsService.java:244
◆ authenticationFormProcessor()
|
inlinestatic |
LoginActionsService(RealmModel realm, EventBuilder event)
Definition: LoginActionsService.java:178
static UriBuilder loginActionsBaseUrl(UriInfo uriInfo)
Definition: LoginActionsService.java:145
◆ brokerLoginFlow()
|
inlineprotected |
729 EventType eventType = firstBrokerLogin ? EventType.IDENTITY_PROVIDER_FIRST_LOGIN : EventType.IDENTITY_PROVIDER_POST_LOGIN;
732 SessionCodeChecks checks = checksForCode(authSessionId, code, execution, clientId, tabId, flowPath);
733 if (!checks.verifyActiveAndValidAction(AuthenticationSessionModel.Action.AUTHENTICATE.name(), ClientSessionCode.ActionType.LOGIN)) {
739 String noteKey = firstBrokerLogin ? AbstractIdpAuthenticator.BROKERED_CONTEXT_NOTE : PostBrokerLoginConstants.PBL_BROKERED_IDENTITY_CONTEXT;
740 SerializedBrokeredIdentityContext serializedCtx = SerializedBrokeredIdentityContext.readFromAuthenticationSession(authSession, noteKey);
743 throw new WebApplicationException(ErrorPage.error(session, authSession, Response.Status.BAD_REQUEST, "Not found serialized context in authenticationSession."));
748 String flowId = firstBrokerLogin ? brokerContext.getIdpConfig().getFirstBrokerLoginFlowId() : brokerContext.getIdpConfig().getPostBrokerLoginFlowId();
751 throw new WebApplicationException(ErrorPage.error(session, authSession, Response.Status.BAD_REQUEST, "Flow not configured for identity provider"));
756 throw new WebApplicationException(ErrorPage.error(session, authSession, Response.Status.BAD_REQUEST, "Flow not found for identity provider"));
768 authSession.setAuthNote(AbstractIdpAuthenticator.FIRST_BROKER_LOGIN_SUCCESS, identityProviderAlias);
770 String authStateNoteKey = PostBrokerLoginConstants.PBL_AUTH_STATE_PREFIX + identityProviderAlias;
779 return processFlow(checks.isActionRequest(), execution, authSession, flowPath, brokerLoginFlow, null, processor);
SessionCodeChecks checksForCode(String authSessionId, String code, String execution, String clientId, String tabId, String flowPath)
Definition: LoginActionsService.java:192
static final String FIRST_BROKER_LOGIN_PATH
Definition: LoginActionsService.java:116
Response brokerLoginFlow(String authSessionId, String code, String execution, String clientId, String tabId, String flowPath)
Definition: LoginActionsService.java:726
Response redirectToAfterBrokerLoginEndpoint(AuthenticationSessionModel authSession, boolean firstBrokerLogin)
Definition: LoginActionsService.java:782
Response processFlow(boolean action, String execution, AuthenticationSessionModel authSession, String flowPath, AuthenticationFlowModel flow, String errorMessage, AuthenticationProcessor processor)
Definition: LoginActionsService.java:266
RealmModel realm
Definition: LoginActionsService.java:126
KeycloakSession session
Definition: LoginActionsService.java:141
◆ checksForCode()
|
inlineprivate |
193 SessionCodeChecks res = new SessionCodeChecks(realm, session.getContext().getUri(), request, clientConnection, session, event, authSessionId, code, execution, clientId, tabId, flowPath);
HttpRequest request
Definition: LoginActionsService.java:129
ClientConnection clientConnection
Definition: LoginActionsService.java:135
EventBuilder event
Definition: LoginActionsService.java:143
RealmModel realm
Definition: LoginActionsService.java:126
KeycloakSession session
Definition: LoginActionsService.java:141
◆ checkSsl()
|
inlineprivate |
ClientConnection clientConnection
Definition: LoginActionsService.java:135
RealmModel realm
Definition: LoginActionsService.java:126
KeycloakSession session
Definition: LoginActionsService.java:141
◆ createAuthenticationSessionForClient()
|
inlinepackage |
381 RootAuthenticationSessionModel rootAuthSession = new AuthenticationSessionManager(session).createAuthenticationSession(realm, true);
387 String redirectUri = Urls.accountBase(session.getContext().getUri().getBaseUri()).path("/").build(realm.getName()).toString();
391 authSession.setClientNote(OIDCLoginProtocol.ISSUER, Urls.realmIssuer(session.getContext().getUri().getBaseUri(), realm.getName()));
RealmModel realm
Definition: LoginActionsService.java:126
KeycloakSession session
Definition: LoginActionsService.java:141
◆ executeActionToken()
|
inline |
Handles a given token using the given token handler. If there is any VerificationException thrown in the handler, it is handled automatically here to reduce boilerplate code.
- 引数
-
key execution
- 戻り値
protected< T extends JsonWebToken &ActionTokenKeyModel > Response handleActionToken(String tokenString, String execution, String clientId, String tabId)
Definition: LoginActionsService.java:435
◆ firstBrokerLoginGet()
|
inline |
692 return brokerLoginFlow(authSessionId, code, execution, clientId, tabId, FIRST_BROKER_LOGIN_PATH);
static final String FIRST_BROKER_LOGIN_PATH
Definition: LoginActionsService.java:116
Response brokerLoginFlow(String authSessionId, String code, String execution, String clientId, String tabId, String flowPath)
Definition: LoginActionsService.java:726
◆ firstBrokerLoginPost()
|
inline |
702 return brokerLoginFlow(authSessionId, code, execution, clientId, tabId, FIRST_BROKER_LOGIN_PATH);
static final String FIRST_BROKER_LOGIN_PATH
Definition: LoginActionsService.java:116
Response brokerLoginFlow(String authSessionId, String code, String execution, String clientId, String tabId, String flowPath)
Definition: LoginActionsService.java:726
◆ firstBrokerLoginProcessor()
|
inlinestatic |
LoginActionsService(RealmModel realm, EventBuilder event)
Definition: LoginActionsService.java:178
static UriBuilder loginActionsBaseUrl(UriInfo uriInfo)
Definition: LoginActionsService.java:145
◆ getLastExecutionUrl()
|
inlineprotected |
RealmModel realm
Definition: LoginActionsService.java:126
KeycloakSession session
Definition: LoginActionsService.java:141
URI getLastExecutionUrl(String flowPath, String executionId, String clientId, String tabId)
Definition: LoginActionsService.java:199
◆ handleActionToken()
|
inlinepackage |
449 AuthenticationSessionManager authenticationSessionManager = new AuthenticationSessionManager(session);
452 authSession = authenticationSessionManager.getCurrentAuthenticationSession(realm, client, tabId);
460 throw new ExplainedTokenVerificationException(null, Errors.NOT_ALLOWED, Messages.INVALID_REQUEST);
463 TokenVerifier<DefaultActionTokenKey> tokenVerifier = TokenVerifier.create(tokenString, DefaultActionTokenKey.class);
476 throw new ExplainedTokenVerificationException(aToken, Errors.REALM_DISABLED, Messages.REALM_NOT_ENABLED);
479 throw new ExplainedTokenVerificationException(aToken, Errors.SSL_REQUIRED, Messages.HTTPS_REQUIRED);
486 new TokenVerifier.RealmUrlCheck(Urls.realmIssuer(session.getContext().getUri().getBaseUri(), realm.getName())),
493 SignatureVerifierContext signatureVerifier = session.getProvider(SignatureProvider.class, algorithm).verifier(kid);
509 return processFlowFromPath(flowPath, authSession, Messages.EXPIRED_ACTION_TOKEN_SESSION_EXISTS);
512 return handleActionTokenVerificationException(null, ex, Errors.EXPIRED_CODE, Messages.EXPIRED_ACTION_TOKEN_NO_SESSION);
522 tokenContext = new ActionTokenContext(session, realm, session.getContext().getUri(), clientConnection, request, event, handler, execution, this::processFlow, this::brokerLoginFlow);
525 String tokenAuthSessionCompoundId = handler.getAuthenticationSessionIdFromToken(token, tokenContext, authSession);
529 String sessionId = AuthenticationSessionCompoundId.encoded(tokenAuthSessionCompoundId).getRootSessionId();
537 ! LoginActionsServiceChecks.doesAuthenticationSessionFromCookieMatchOneFromToken(tokenContext, authSession, tokenAuthSessionCompoundId)) {
538 // There exists an authentication session but no auth session ID was received in the action token
539 logger.debugf("Authentication session in progress but no authentication session ID was found in action token %s, restarting.", token.getId());
573 return handleActionTokenVerificationException(tokenContext, ex, ex.getErrorEvent(), ex.getMessage());
580 return handleActionTokenVerificationException(tokenContext, ex, eventError, defaultErrorMessage);
private< T extends JsonWebToken > ActionTokenHandler< T > resolveActionTokenHandler(String actionId)
Definition: LoginActionsService.java:596
Response processFlowFromPath(String flowPath, AuthenticationSessionModel authSession, String errorMessage)
Definition: LoginActionsService.java:584
HttpRequest request
Definition: LoginActionsService.java:129
void initLoginEvent(AuthenticationSessionModel authSession)
Definition: LoginActionsService.java:870
ClientConnection clientConnection
Definition: LoginActionsService.java:135
EventBuilder event
Definition: LoginActionsService.java:143
boolean checkSsl()
Definition: LoginActionsService.java:184
static final String AUTHENTICATE_PATH
Definition: LoginActionsService.java:112
RealmModel realm
Definition: LoginActionsService.java:126
Response handleActionTokenVerificationException(ActionTokenContext<?> tokenContext, VerificationException ex, String eventError, String errorMessage)
Definition: LoginActionsService.java:608
KeycloakSession session
Definition: LoginActionsService.java:141
static final Logger logger
Definition: LoginActionsService.java:110
String getDefaultEventError()
◆ handleActionTokenVerificationException()
|
inlineprivate |
610 new AuthenticationSessionManager(session).removeAuthenticationSession(realm, tokenContext.getAuthenticationSession(), true);
616 return ErrorPage.error(session, null, Response.Status.BAD_REQUEST, errorMessage == null ? Messages.INVALID_CODE : errorMessage);
AuthenticationSessionModel getAuthenticationSession()
Definition: ActionTokenContext.java:134
RealmModel realm
Definition: LoginActionsService.java:126
KeycloakSession session
Definition: LoginActionsService.java:141
◆ initLoginEvent()
|
inlineprivate |
876 OIDCResponseMode responseMode = OIDCResponseMode.parse(respMode, OIDCResponseType.parse(responseType));
891 String attemptedUsername = authSession.getAuthNote(AbstractUsernameFormAuthenticator.ATTEMPTED_USERNAME);
◆ loginActionsBaseUrl() [1/2]
|
inlinestatic |
static UriBuilder loginActionsBaseUrl(UriInfo uriInfo)
Definition: LoginActionsService.java:145
◆ loginActionsBaseUrl() [2/2]
|
inlinestatic |
◆ postBrokerLoginGet()
|
inline |
712 return brokerLoginFlow(authSessionId, code, execution, clientId, tabId, POST_BROKER_LOGIN_PATH);
Response brokerLoginFlow(String authSessionId, String code, String execution, String clientId, String tabId, String flowPath)
Definition: LoginActionsService.java:726
static final String POST_BROKER_LOGIN_PATH
Definition: LoginActionsService.java:117
◆ postBrokerLoginPost()
|
inline |
722 return brokerLoginFlow(authSessionId, code, execution, clientId, tabId, POST_BROKER_LOGIN_PATH);
Response brokerLoginFlow(String authSessionId, String code, String execution, String clientId, String tabId, String flowPath)
Definition: LoginActionsService.java:726
static final String POST_BROKER_LOGIN_PATH
Definition: LoginActionsService.java:117
◆ postBrokerLoginProcessor()
|
inlinestatic |
LoginActionsService(RealmModel realm, EventBuilder event)
Definition: LoginActionsService.java:178
static UriBuilder loginActionsBaseUrl(UriInfo uriInfo)
Definition: LoginActionsService.java:145
◆ processAuthentication()
|
inlineprotected |
263 return processFlow(action, execution, authSession, AUTHENTICATE_PATH, AuthenticationFlowResolver.resolveBrowserFlow(authSession), errorMessage, new AuthenticationProcessor());
Response processFlow(boolean action, String execution, AuthenticationSessionModel authSession, String flowPath, AuthenticationFlowModel flow, String errorMessage, AuthenticationProcessor processor)
Definition: LoginActionsService.java:266
static final String AUTHENTICATE_PATH
Definition: LoginActionsService.java:112
◆ processConsent()
|
inline |
OAuth grant page. You should not invoked this directly!
- 引数
-
formData
- 戻り値
812 String clientId = session.getContext().getUri().getQueryParameters().getFirst(Constants.CLIENT_ID);
838 UserConsentModel grantedConsent = session.users().getConsentByClient(realm, user.getId(), client.getId());
844 // Update may not be required if all clientScopes were already granted (May happen for example with prompt=consent)
866 ClientSessionContext clientSessionCtx = AuthenticationProcessor.attachSession(authSession, null, session, realm, clientConnection, event);
867 return AuthenticationManager.redirectAfterSuccessfulFlow(session, realm, clientSessionCtx.getClientSession().getUserSession(), clientSessionCtx, request, session.getContext().getUri(), clientConnection, event, authSession.getProtocol());
SessionCodeChecks checksForCode(String authSessionId, String code, String execution, String clientId, String tabId, String flowPath)
Definition: LoginActionsService.java:192
HttpRequest request
Definition: LoginActionsService.java:129
void initLoginEvent(AuthenticationSessionModel authSession)
Definition: LoginActionsService.java:870
ClientConnection clientConnection
Definition: LoginActionsService.java:135
HttpHeaders headers
Definition: LoginActionsService.java:132
EventBuilder event
Definition: LoginActionsService.java:143
static final String SESSION_CODE
Definition: LoginActionsService.java:123
static final String REQUIRED_ACTION
Definition: LoginActionsService.java:115
RealmModel realm
Definition: LoginActionsService.java:126
KeycloakSession session
Definition: LoginActionsService.java:141
static final Logger logger
Definition: LoginActionsService.java:110
◆ processFlow()
|
inlineprotected |
304 return BrowserHistoryHelper.getInstance().saveResponseAndRedirect(session, authSession, response, action, request);
static final String FORWARDED_ERROR_MESSAGE_NOTE
Definition: LoginActionsService.java:121
HttpRequest request
Definition: LoginActionsService.java:129
ClientConnection clientConnection
Definition: LoginActionsService.java:135
EventBuilder event
Definition: LoginActionsService.java:143
RealmModel realm
Definition: LoginActionsService.java:126
KeycloakSession session
Definition: LoginActionsService.java:141
◆ processFlowFromPath()
|
inlineprivate |
592 return ErrorPage.error(session, authSession, Response.Status.BAD_REQUEST, errorMessage == null ? Messages.INVALID_REQUEST : errorMessage);
Response processAuthentication(boolean action, String execution, AuthenticationSessionModel authSession, String errorMessage)
Definition: LoginActionsService.java:262
static final String REGISTRATION_PATH
Definition: LoginActionsService.java:113
Response processRegistration(boolean action, String execution, AuthenticationSessionModel authSession, String errorMessage)
Definition: LoginActionsService.java:626
static final String RESET_CREDENTIALS_PATH
Definition: LoginActionsService.java:114
static final String AUTHENTICATE_PATH
Definition: LoginActionsService.java:112
Response processResetCredentials(boolean actionRequest, String execution, AuthenticationSessionModel authSession, String errorMessage)
Definition: LoginActionsService.java:619
KeycloakSession session
Definition: LoginActionsService.java:141
◆ processRegister()
|
inline |
Registration
- 引数
-
code
- 戻り値
Response registerRequest(String authSessionId, String code, String execution, String clientId, String tabId, boolean isPostRequest)
Definition: LoginActionsService.java:665
◆ processRegistration()
|
inlineprotected |
627 return processFlow(action, execution, authSession, REGISTRATION_PATH, realm.getRegistrationFlow(), errorMessage, new AuthenticationProcessor());
static final String REGISTRATION_PATH
Definition: LoginActionsService.java:113
Response processFlow(boolean action, String execution, AuthenticationSessionModel authSession, String flowPath, AuthenticationFlowModel flow, String errorMessage, AuthenticationProcessor processor)
Definition: LoginActionsService.java:266
RealmModel realm
Definition: LoginActionsService.java:126
◆ processRequireAction()
|
inlineprivate |
933 SessionCodeChecks checks = checksForCode(authSessionId, code, action, clientId, tabId, REQUIRED_ACTION);
942 return AuthenticationManager.nextActionAfterAuthentication(session, authSession, clientConnection, request, session.getContext().getUri(), event);
949 RequiredActionFactory factory = (RequiredActionFactory)session.getKeycloakSessionFactory().getProviderFactory(RequiredActionProvider.class, action);
953 throw new WebApplicationException(ErrorPage.error(session, authSession, Response.Status.BAD_REQUEST, Messages.INVALID_CODE));
955 RequiredActionContextResult context = new RequiredActionContextResult(authSession, realm, event, session, request, authSession.getAuthenticatedUser(), factory) {
968 throw new WebApplicationException(ErrorPage.error(session, authSession, Response.Status.BAD_REQUEST, Messages.DISPLAY_UNSUPPORTED));
987 response = AuthenticationManager.nextActionAfterAuthentication(session, authSession, clientConnection, request, session.getContext().getUri(), event);
991 LoginProtocol protocol = context.getSession().getProvider(LoginProtocol.class, authSession.getProtocol());
1004 return BrowserHistoryHelper.getInstance().saveResponseAndRedirect(session, authSession, response, true, request);
SessionCodeChecks checksForCode(String authSessionId, String code, String execution, String clientId, String tabId, String flowPath)
Definition: LoginActionsService.java:192
HttpRequest request
Definition: LoginActionsService.java:129
void initLoginEvent(AuthenticationSessionModel authSession)
Definition: LoginActionsService.java:870
ClientConnection clientConnection
Definition: LoginActionsService.java:135
EventBuilder event
Definition: LoginActionsService.java:143
static final String REQUIRED_ACTION
Definition: LoginActionsService.java:115
RealmModel realm
Definition: LoginActionsService.java:126
KeycloakSession session
Definition: LoginActionsService.java:141
◆ processResetCredentials()
|
inlineprotected |
620 AuthenticationProcessor authProcessor = new ResetCredentialsActionTokenHandler.ResetCredsAuthenticationProcessor();
622 return processFlow(actionRequest, execution, authSession, RESET_CREDENTIALS_PATH, realm.getResetCredentialsFlow(), errorMessage, authProcessor);
static final String RESET_CREDENTIALS_PATH
Definition: LoginActionsService.java:114
Response processFlow(boolean action, String execution, AuthenticationSessionModel authSession, String flowPath, AuthenticationFlowModel flow, String errorMessage, AuthenticationProcessor processor)
Definition: LoginActionsService.java:266
RealmModel realm
Definition: LoginActionsService.java:126
◆ redirectToAfterBrokerLoginEndpoint() [1/2]
|
inlineprivate |
783 return redirectToAfterBrokerLoginEndpoint(session, realm, session.getContext().getUri(), authSession, firstBrokerLogin);
Response redirectToAfterBrokerLoginEndpoint(AuthenticationSessionModel authSession, boolean firstBrokerLogin)
Definition: LoginActionsService.java:782
RealmModel realm
Definition: LoginActionsService.java:126
KeycloakSession session
Definition: LoginActionsService.java:141
◆ redirectToAfterBrokerLoginEndpoint() [2/2]
|
inlinestatic |
787 ClientSessionCode<AuthenticationSessionModel> accessCode = new ClientSessionCode<>(session, realm, authSession);
792 URI redirect = firstBrokerLogin ? Urls.identityProviderAfterFirstBrokerLogin(uriInfo.getBaseUri(), realm.getName(), accessCode.getOrGenerateCode(), clientId, tabId) :
793 Urls.identityProviderAfterPostBrokerLogin(uriInfo.getBaseUri(), realm.getName(), accessCode.getOrGenerateCode(), clientId, tabId) ;
RealmModel realm
Definition: LoginActionsService.java:126
KeycloakSession session
Definition: LoginActionsService.java:141
static final Logger logger
Definition: LoginActionsService.java:110
◆ registerPage()
|
inline |
protocol independent registration page entry point
- 引数
-
code
- 戻り値
Response registerRequest(String authSessionId, String code, String execution, String clientId, String tabId, boolean isPostRequest)
Definition: LoginActionsService.java:665
◆ registerRequest()
|
inlineprivate |
669 return ErrorPage.error(session, null, Response.Status.BAD_REQUEST, Messages.REGISTRATION_NOT_ALLOWED);
672 SessionCodeChecks checks = checksForCode(authSessionId, code, execution, clientId, tabId, REGISTRATION_PATH);
673 if (!checks.verifyActiveAndValidAction(AuthenticationSessionModel.Action.AUTHENTICATE.name(), ClientSessionCode.ActionType.LOGIN)) {
679 AuthenticationManager.expireIdentityCookie(realm, session.getContext().getUri(), clientConnection);
SessionCodeChecks checksForCode(String authSessionId, String code, String execution, String clientId, String tabId, String flowPath)
Definition: LoginActionsService.java:192
static final String REGISTRATION_PATH
Definition: LoginActionsService.java:113
ClientConnection clientConnection
Definition: LoginActionsService.java:135
Response processRegistration(boolean action, String execution, AuthenticationSessionModel authSession, String errorMessage)
Definition: LoginActionsService.java:626
RealmModel realm
Definition: LoginActionsService.java:126
KeycloakSession session
Definition: LoginActionsService.java:141
◆ registrationFormProcessor()
|
inlinestatic |
LoginActionsService(RealmModel realm, EventBuilder event)
Definition: LoginActionsService.java:178
static UriBuilder loginActionsBaseUrl(UriInfo uriInfo)
Definition: LoginActionsService.java:145
◆ requiredActionGET()
|
inline |
Response processRequireAction(final String authSessionId, final String code, String action, String clientId, String tabId)
Definition: LoginActionsService.java:930
◆ requiredActionPOST()
|
inline |
Response processRequireAction(final String authSessionId, final String code, String action, String clientId, String tabId)
Definition: LoginActionsService.java:930
◆ requiredActionProcessor()
|
inlinestatic |
LoginActionsService(RealmModel realm, EventBuilder event)
Definition: LoginActionsService.java:178
static UriBuilder loginActionsBaseUrl(UriInfo uriInfo)
Definition: LoginActionsService.java:145
◆ resetCredentials()
|
inlineprotected |
- 引数
-
code execution
- 戻り値
402 SessionCodeChecks checks = checksForCode(authSessionId, code, execution, clientId, tabId, RESET_CREDENTIALS_PATH);
403 if (!checks.verifyActiveAndValidAction(AuthenticationSessionModel.Action.AUTHENTICATE.name(), ClientSessionCode.ActionType.USER)) {
410 return ErrorPage.error(session, authSession, Response.Status.BAD_REQUEST, Messages.RESET_CREDENTIAL_NOT_ALLOWED);
SessionCodeChecks checksForCode(String authSessionId, String code, String execution, String clientId, String tabId, String flowPath)
Definition: LoginActionsService.java:192
static final String RESET_CREDENTIALS_PATH
Definition: LoginActionsService.java:114
RealmModel realm
Definition: LoginActionsService.java:126
Response processResetCredentials(boolean actionRequest, String execution, AuthenticationSessionModel authSession, String errorMessage)
Definition: LoginActionsService.java:619
KeycloakSession session
Definition: LoginActionsService.java:141
◆ resetCredentialsGET()
|
inline |
Endpoint for executing reset credentials flow. If token is null, a authentication session is created with the account service as the client. Successful reset sends you to the account page. Note, account service must be enabled.
- 引数
-
code execution
- 戻り値
356 AuthenticationSessionModel authSession = new AuthenticationSessionManager(session).getCurrentAuthenticationSession(realm, client, tabId);
358 // we allow applications to link to reset credentials without going through OAuth or SAML handshakes
363 return ErrorPage.error(session, authSession, Response.Status.BAD_REQUEST, Messages.RESET_CREDENTIAL_NOT_ALLOWED);
Response resetCredentials(String authSessionId, String code, String execution, String clientId, String tabId)
Definition: LoginActionsService.java:401
RealmModel realm
Definition: LoginActionsService.java:126
Response processResetCredentials(boolean actionRequest, String execution, AuthenticationSessionModel authSession, String errorMessage)
Definition: LoginActionsService.java:619
KeycloakSession session
Definition: LoginActionsService.java:141
AuthenticationSessionModel createAuthenticationSessionForClient()
Definition: LoginActionsService.java:374
◆ resetCredentialsPOST()
|
inline |
protected< T extends JsonWebToken &ActionTokenKeyModel > Response handleActionToken(String tokenString, String execution, String clientId, String tabId)
Definition: LoginActionsService.java:435
Response resetCredentials(String authSessionId, String code, String execution, String clientId, String tabId)
Definition: LoginActionsService.java:401
◆ resolveActionTokenHandler()
|
inlinepackage |
KeycloakSession session
Definition: LoginActionsService.java:141
◆ restartSession()
|
inline |
protocol independent page for restart of the flow
- 戻り値
216 SessionCodeChecks checks = new SessionCodeChecks(realm, session.getContext().getUri(), request, clientConnection, session, event, authSessionId, null, null, clientId, tabId, null);
230 URI redirectUri = getLastExecutionUrl(flowPath, null, authSession.getClient().getClientId(), tabId);
HttpRequest request
Definition: LoginActionsService.java:129
ClientConnection clientConnection
Definition: LoginActionsService.java:135
EventBuilder event
Definition: LoginActionsService.java:143
static final String AUTHENTICATE_PATH
Definition: LoginActionsService.java:112
RealmModel realm
Definition: LoginActionsService.java:126
KeycloakSession session
Definition: LoginActionsService.java:141
URI getLastExecutionUrl(String flowPath, String executionId, String clientId, String tabId)
Definition: LoginActionsService.java:199
static final Logger logger
Definition: LoginActionsService.java:110
メンバ詳解
◆ AUTH_SESSION_ID
|
static |
◆ AUTHENTICATE_PATH
|
static |
◆ clientConnection
|
private |
◆ event
|
private |
◆ FIRST_BROKER_LOGIN_PATH
|
static |
◆ FORWARDED_ERROR_MESSAGE_NOTE
|
static |
◆ headers
|
protected |
◆ logger
|
staticprivate |
◆ POST_BROKER_LOGIN_PATH
|
static |
◆ providers
|
protected |
◆ realm
|
private |
◆ REGISTRATION_PATH
|
static |
◆ request
|
private |
◆ REQUIRED_ACTION
|
static |
◆ RESET_CREDENTIALS_PATH
|
static |
◆ RESTART_PATH
|
static |
◆ session
|
protected |
◆ SESSION_CODE
|
static |
このクラス詳解は次のファイルから抽出されました:
- D:/AppData/doxygen/keycloak/rest-service/src/services/src/main/java/org/keycloak/services/resources/LoginActionsService.java
 1.8.13
1.8.13