org.keycloak.protocol.oidc.endpoints.UserInfoEndpoint 連携図
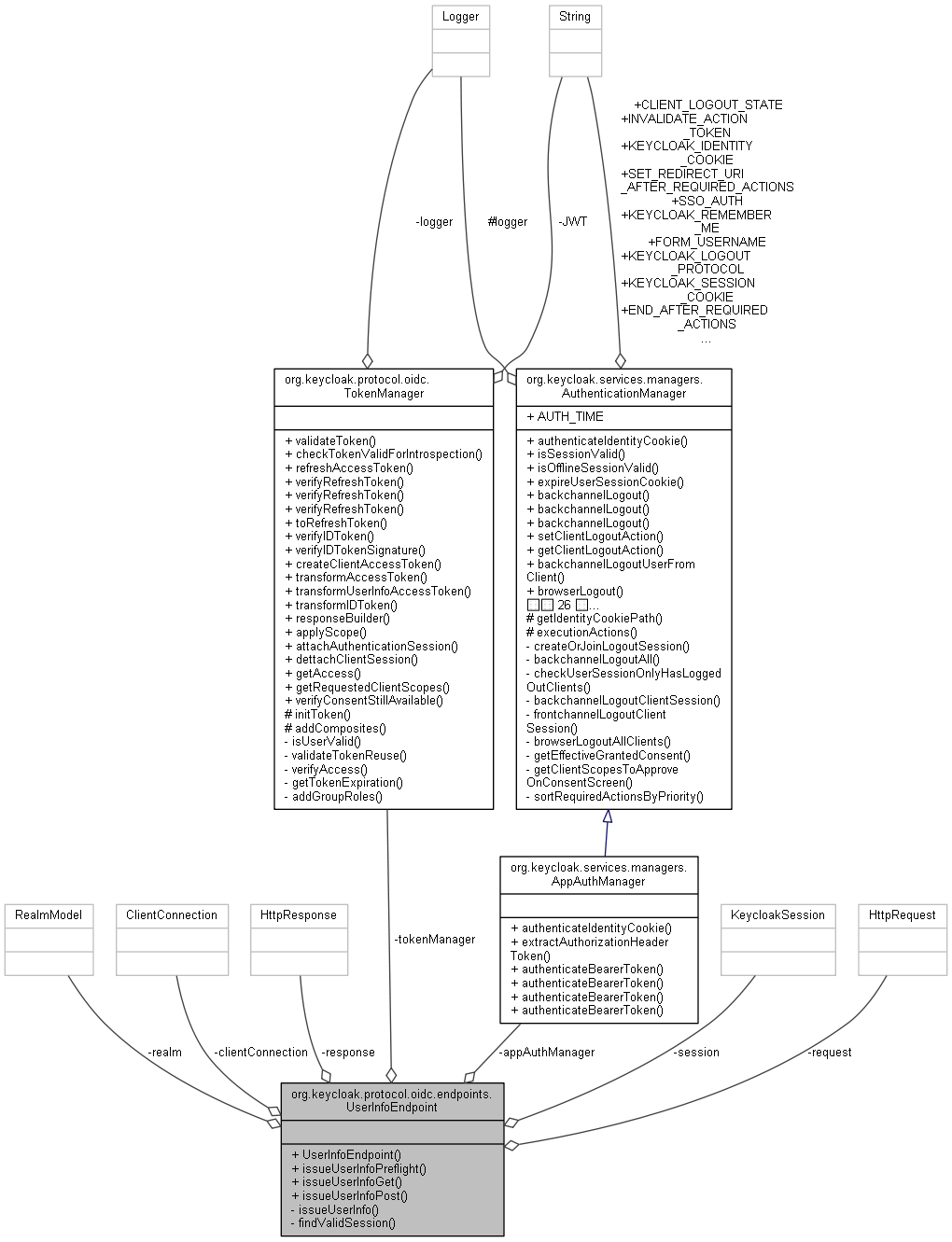
公開メンバ関数 | |
| UserInfoEndpoint (org.keycloak.protocol.oidc.TokenManager tokenManager, RealmModel realm) | |
| Response | issueUserInfoPreflight () |
| Response | issueUserInfoGet (@Context final HttpHeaders headers) |
| Response | issueUserInfoPost () |
非公開メンバ関数 | |
| Response | issueUserInfo (String tokenString) |
| UserSessionModel | findValidSession (AccessToken token, EventBuilder event, ClientModel client) |
非公開変数類 | |
| HttpRequest | request |
| HttpResponse | response |
| KeycloakSession | session |
| ClientConnection | clientConnection |
| final org.keycloak.protocol.oidc.TokenManager | tokenManager |
| final AppAuthManager | appAuthManager |
| final RealmModel | realm |
詳解
構築子と解体子
◆ UserInfoEndpoint()
|
inline |
final org.keycloak.protocol.oidc.TokenManager tokenManager
Definition: UserInfoEndpoint.java:82
final RealmModel realm
Definition: UserInfoEndpoint.java:84
final AppAuthManager appAuthManager
Definition: UserInfoEndpoint.java:83
関数詳解
◆ findValidSession()
|
inlineprivate |
227 UserSessionModel userSession = new UserSessionCrossDCManager(session).getUserSessionWithClient(realm, token.getSessionState(), false, client.getId());
233 offlineUserSession = new UserSessionCrossDCManager(session).getUserSessionWithClient(realm, token.getSessionState(), true, client.getId());
242 throw new ErrorResponseException(OAuthErrorException.INVALID_REQUEST, "User session not found or doesn't have client attached on it", Response.Status.UNAUTHORIZED);
252 throw new ErrorResponseException(OAuthErrorException.INVALID_TOKEN, "Session expired", Response.Status.UNAUTHORIZED);
final RealmModel realm
Definition: UserInfoEndpoint.java:84
KeycloakSession session
Definition: UserInfoEndpoint.java:77
◆ issueUserInfo()
|
inlineprivate |
129 throw new ErrorResponseException(OAuthErrorException.INVALID_REQUEST, "Token not provided", Response.Status.BAD_REQUEST);
137 SignatureVerifierContext verifierContext = session.getProvider(SignatureProvider.class, verifier.getHeader().getAlgorithm().name()).verifier(verifier.getHeader().getKeyId());
143 throw new ErrorResponseException(OAuthErrorException.INVALID_TOKEN, "Token invalid: " + e.getMessage(), Response.Status.UNAUTHORIZED);
149 throw new ErrorResponseException(OAuthErrorException.INVALID_REQUEST, "Client not found", Response.Status.BAD_REQUEST);
158 throw new ErrorResponseException(OAuthErrorException.INVALID_REQUEST, "Client disabled", Response.Status.BAD_REQUEST);
166 throw new ErrorResponseException(OAuthErrorException.INVALID_REQUEST, "User not found", Response.Status.BAD_REQUEST);
177 throw new ErrorResponseException(OAuthErrorException.UNAUTHORIZED_CLIENT, "Client certificate missing, or its thumbprint and one in the refresh token did NOT match", Response.Status.UNAUTHORIZED);
182 AuthenticatedClientSessionModel clientSession = userSession.getAuthenticatedClientSessionByClient(clientModel.getId());
185 ClientSessionContext clientSessionCtx = DefaultClientSessionContext.fromClientSessionScopeParameter(clientSession);
198 String issuerUrl = Urls.realmIssuer(session.getContext().getUri().getBaseUri(), realm.getName());
205 SignatureProvider signatureProvider = session.getProvider(SignatureProvider.class, signatureAlgorithm);
210 responseBuilder = Response.ok(signedUserInfo).header(HttpHeaders.CONTENT_TYPE, MediaType.APPLICATION_JWT);
215 responseBuilder = Response.ok(claims).header(HttpHeaders.CONTENT_TYPE, MediaType.APPLICATION_JSON);
final org.keycloak.protocol.oidc.TokenManager tokenManager
Definition: UserInfoEndpoint.java:82
final RealmModel realm
Definition: UserInfoEndpoint.java:84
KeycloakSession session
Definition: UserInfoEndpoint.java:77
ClientConnection clientConnection
Definition: UserInfoEndpoint.java:80
UserSessionModel findValidSession(AccessToken token, EventBuilder event, ClientModel client)
Definition: UserInfoEndpoint.java:226
HttpRequest request
Definition: UserInfoEndpoint.java:71
AccessToken transformUserInfoAccessToken(KeycloakSession session, AccessToken token, UserSessionModel userSession, ClientSessionContext clientSessionCtx)
Definition: TokenManager.java:613
◆ issueUserInfoGet()
|
inline |
final AppAuthManager appAuthManager
Definition: UserInfoEndpoint.java:83
String extractAuthorizationHeaderToken(HttpHeaders headers)
Definition: AppAuthManager.java:44
Response issueUserInfo(String tokenString)
Definition: UserInfoEndpoint.java:122
◆ issueUserInfoPost()
|
inline |
final AppAuthManager appAuthManager
Definition: UserInfoEndpoint.java:83
String extractAuthorizationHeaderToken(HttpHeaders headers)
Definition: AppAuthManager.java:44
Response issueUserInfo(String tokenString)
Definition: UserInfoEndpoint.java:122
HttpRequest request
Definition: UserInfoEndpoint.java:71
◆ issueUserInfoPreflight()
|
inline |
HttpRequest request
Definition: UserInfoEndpoint.java:71
メンバ詳解
◆ appAuthManager
|
private |
◆ clientConnection
|
private |
◆ realm
|
private |
◆ request
|
private |
◆ response
|
private |
◆ session
|
private |
◆ tokenManager
|
private |
このクラス詳解は次のファイルから抽出されました:
- D:/AppData/doxygen/keycloak/rest-service/src/services/src/main/java/org/keycloak/protocol/oidc/endpoints/UserInfoEndpoint.java
 1.8.13
1.8.13